Building a Career in the Blue Team: The Journey to Becoming a Defensive Cybersecurity Expert
In the world of cybersecurity, the Blue Team plays a vital role in defending organizations against cyber threats. As the guardians of digital assets, ...
281 articles on cybersecurity tips, tutorials, and beginner guides.

In the world of cybersecurity, the Blue Team plays a vital role in defending organizations against cyber threats. As the guardians of digital assets, ...

In the world of cybersecurity, the Red Team and Blue Team are often seen as adversaries—one simulating attacks to identify vulnerabilities, the other ...

The cybersecurity landscape is divided into two primary roles: defensive and offensive. Defensive cybersecurity focuses on protecting systems, data, a...

Cybersecurity is one of the most exciting and rapidly growing fields in technology today, and it's never too early to start exploring it. For middle s...

As technology continues to evolve, the demand for skilled cybersecurity professionals is higher than ever. For students pursuing a degree in cybersecu...

In today’s competitive job market, hands-on experience has become a critical component of education, especially in technical fields such as cybersecur...

1. Introduction Network ports are entry points through which data flows between a computer and the internet or other devices on a network. Some ports ...
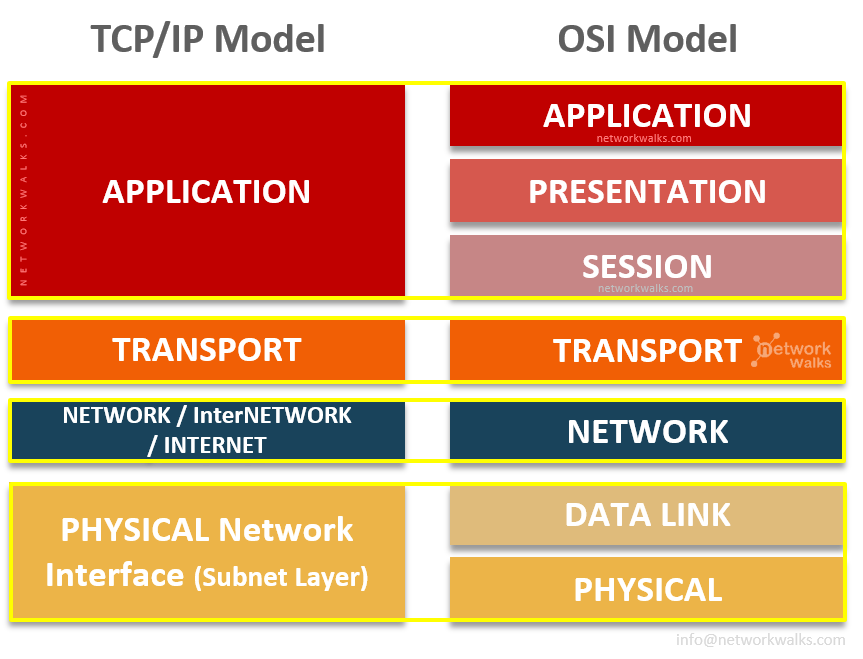
When diving into the world of cybersecurity, one of the fundamental concepts that every hacker, penetration tester, and security professional must und...

Categories of Tools for Cybersecurity and OSINT Assessments Cybersecurity and Open-Source Intelligence (OSINT) are essential fields in today’s digital...

Cybersecurity and Open-Source Intelligence (OSINT) are essential fields in today’s digital landscape, requiring various tools to gather information, a...

In today's rapidly evolving threat landscape, cybersecurity professionals must stay ahead of attackers by utilizing cutting-edge technologies. Kuberne...
Are Your Smart Home Devices Secure? Take Our Privacy Quiz to Find Out! Smart home devices have revolutionized the way we live, making our homes more.....