Overview of Wireshark and other sniffers
Overview of Wireshark Wireshark is a leading open-source network protocol analyzer that allows you to capture and interactively browse the traffic run...
281 articles on cybersecurity tips, tutorials, and beginner guides.

Overview of Wireshark Wireshark is a leading open-source network protocol analyzer that allows you to capture and interactively browse the traffic run...
Cyber Compass GPT: ChatGPT A conversational AI system that listens, learns, and challenges ChatGPT For the Certified Ethical Hacker (CEH) exam, it's e...
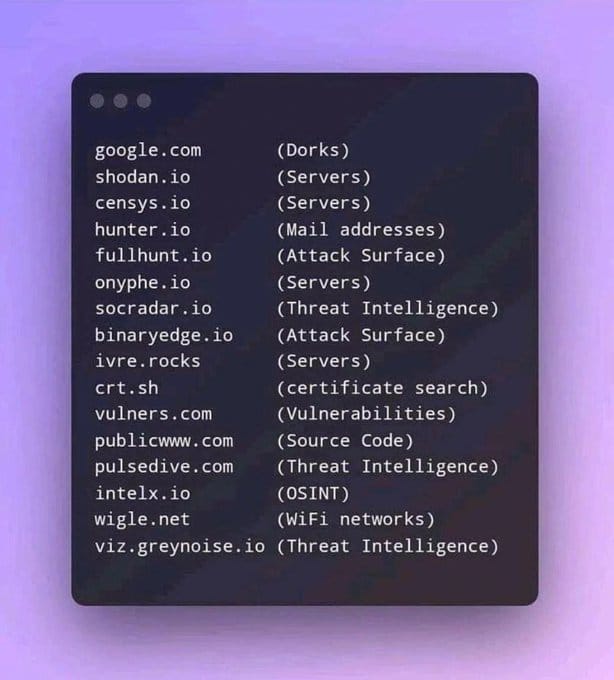
Introduction Open Source Intelligence (OSINT) tools are invaluable for cybersecurity professionals and enthusiasts alike. These tools allow users to g...

Container security is a multi-faceted discipline focusing on securing containerized applications and the environments they run in. Below, I'll expand ...

In today's interconnected digital landscape, full-stack development plays a crucial role in building robust, efficient, and secure applications. The i...

The rise of artificial intelligence (AI) has significantly impacted various sectors, including the gaming industry. AI tools like ChatGPT are being us...
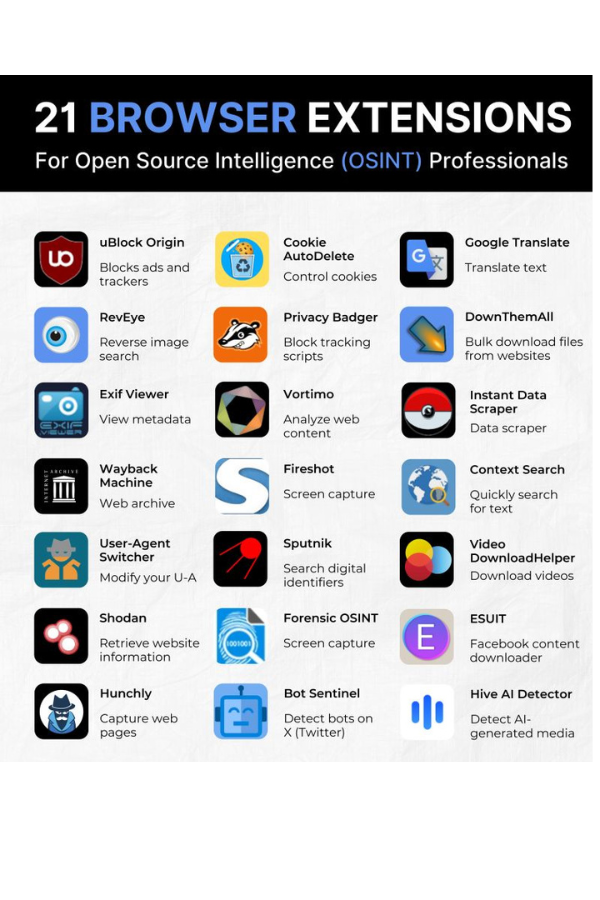
Introduction Open Source Intelligence (OSINT) professionals rely heavily on web browsers for their investigations. Browser extensions can significantl...
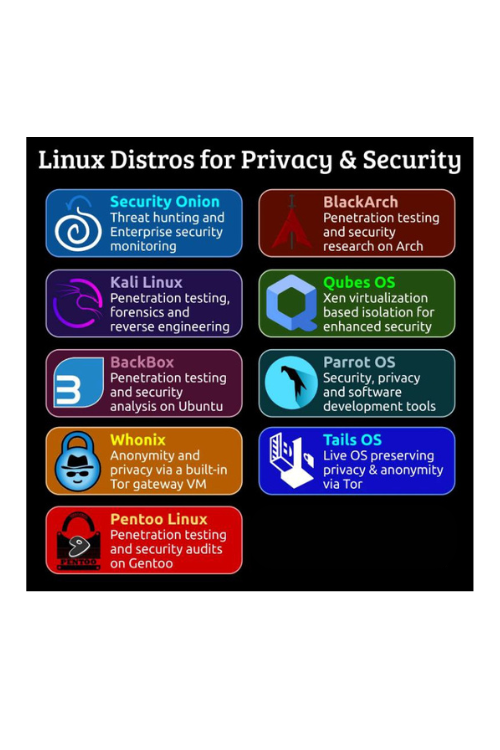
In the realm of cybersecurity, specialized Linux distributions play a crucial role in providing robust platforms for various security tasks. This guid...

In today's digital landscape, cybersecurity is more critical than ever. Organizations and individuals alike need a robust set of tools to protect agai...
In today's digital world, cybersecurity isn't just a technical skill—it's a crucial life skill. With cyber threats growing more sophisticated by the d...

Protecting Your Privacy with DeleteMe: Removing Your Information from People Search and Data Broker Websites In today’s digital age, personal privacy ...
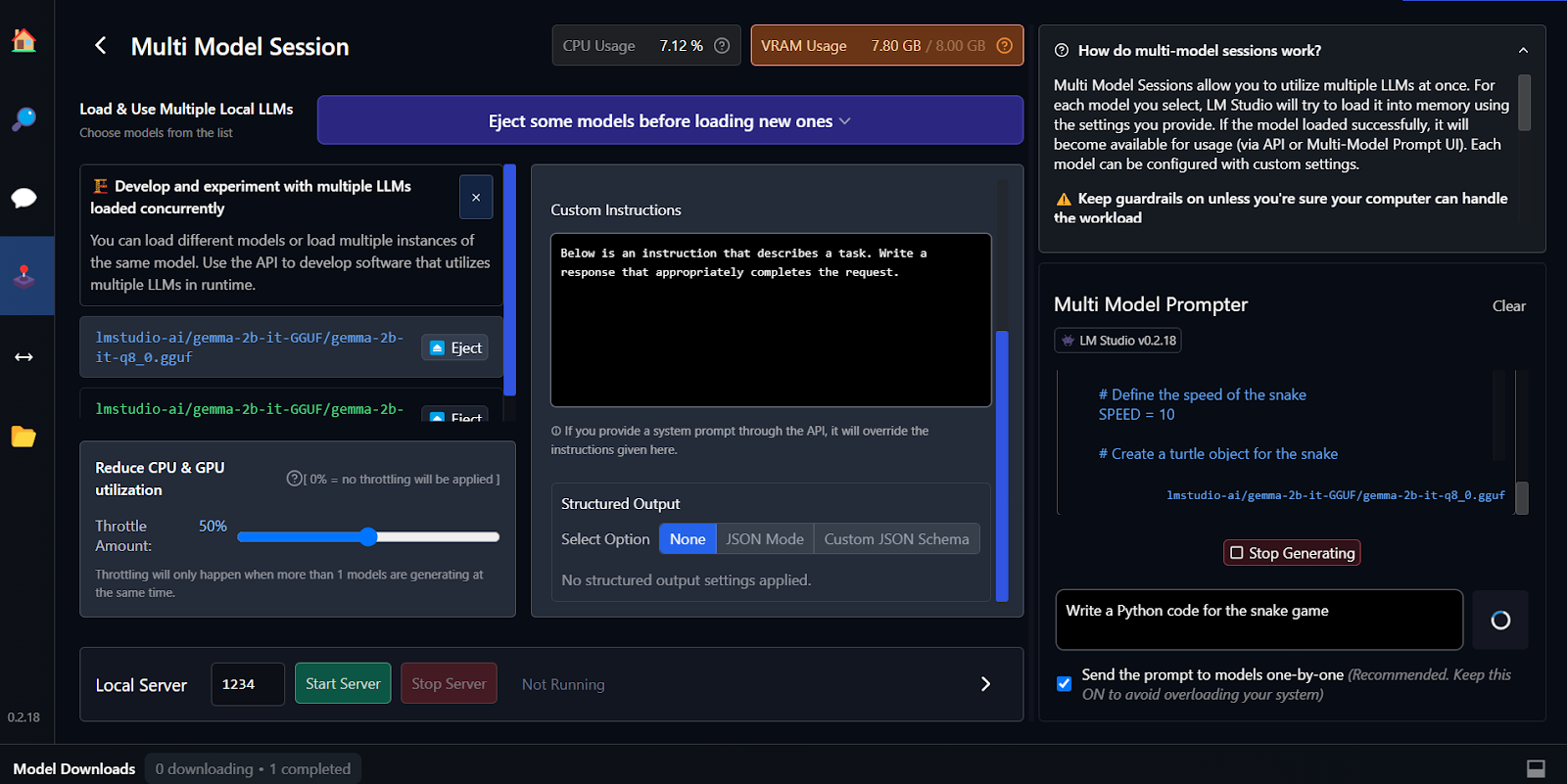
With the increasing capabilities of large language models (LLMs) and the desire for privacy and control, many enthusiasts and professionals are lookin...