AI Weekly Roundup: Major Industry Moves Reshape the Landscape
Artificial Intelligence (AI) has undergone a remarkable transformation since its inception, evolving from theoretical concepts to practical applicatio...
281 articles on cybersecurity tips, tutorials, and beginner guides.
Artificial Intelligence (AI) has undergone a remarkable transformation since its inception, evolving from theoretical concepts to practical applicatio...

Facial recognition technology has become a cornerstone in various industries, from law enforcement to marketing, offering unique insights and efficien...
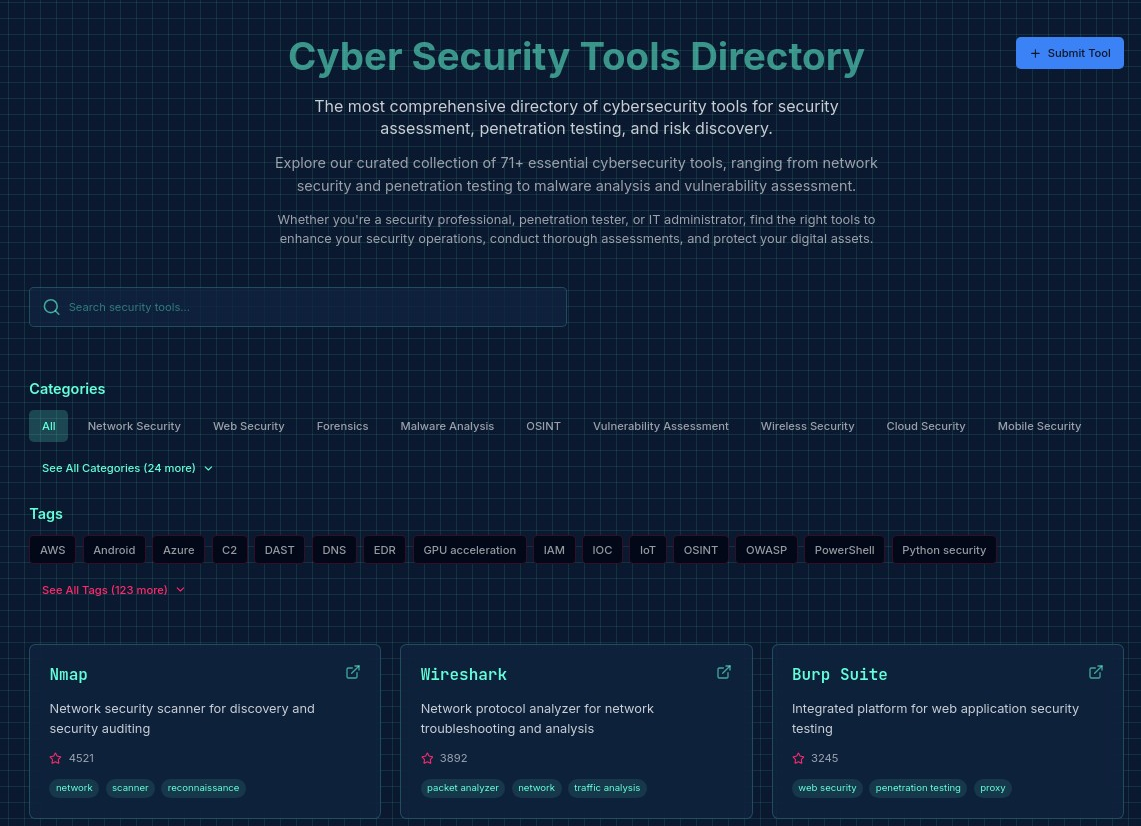
The cybersecurity landscape is a dynamic and challenging environment, with new threats emerging daily and innovative solutions continuously developed ...
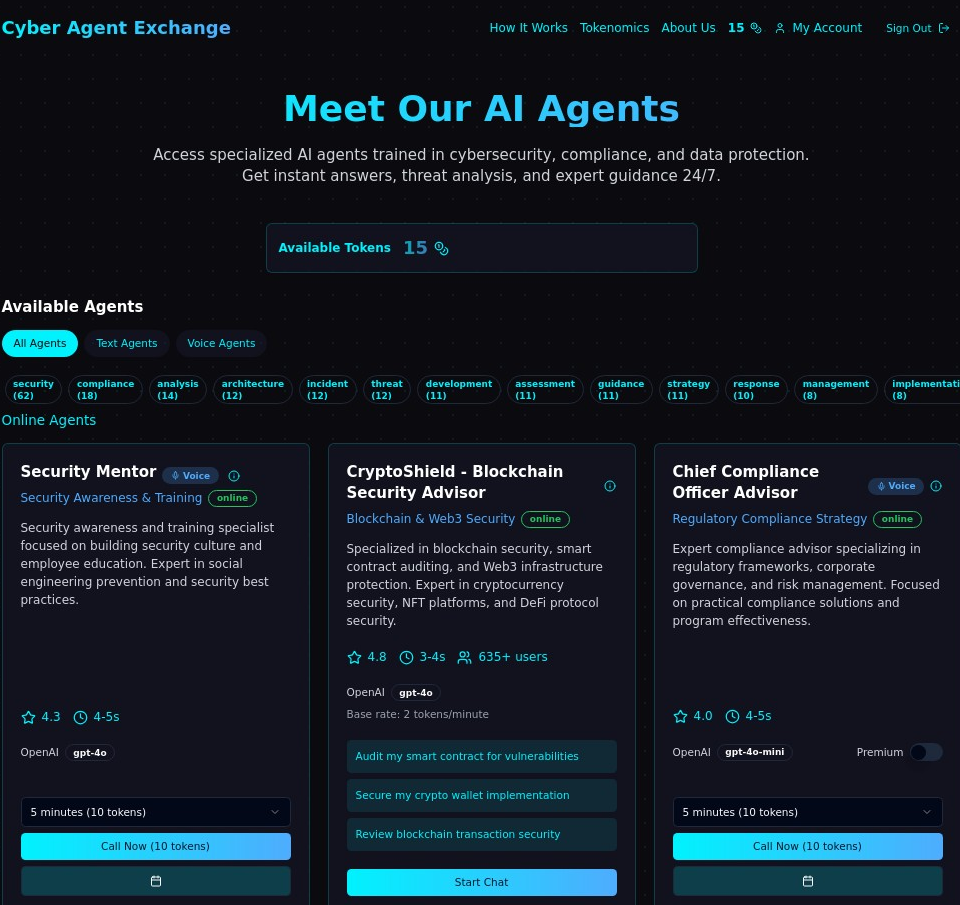
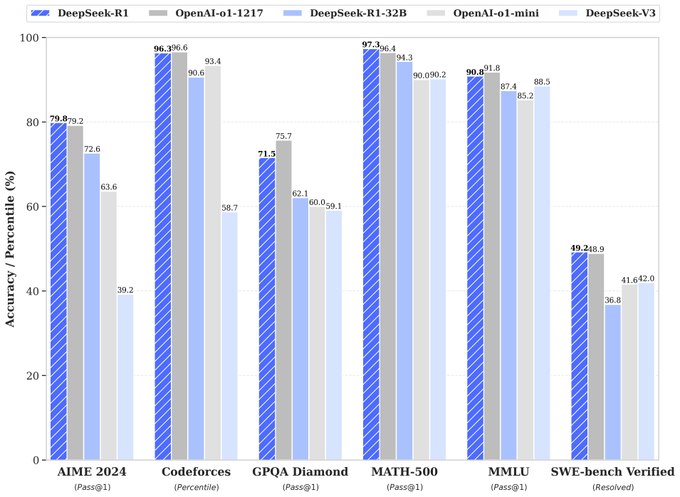
In the ever-evolving field of cybersecurity, artificial intelligence (AI) has become a crucial component in enhancing digital defense mechanisms. Two ...

In an era where digital security is paramount, password strength is one of the most crucial lines of defense against cyber threats. Weak passwords are...

In today's interconnected world, collaboration tools like Microsoft Teams have become essential for remote work and communication. With this rise in u...

Introduction Incident response (IR) is a critical aspect of cybersecurity, especially for Windows-based environments, which are often prime targets fo...
Introduction Incident response (IR) is a critical process in cybersecurity that involves detecting, investigating, and mitigating the impact of securi...

Open Source Intelligence (OSINT) and penetration testing often require effective tools to streamline data gathering, reconnaissance, and analysis. Web...

Introduction Open Source Intelligence (OSINT) is the practice of gathering, analyzing, and using publicly available information to support decision-ma...

A recent report from OpenAI has revealed that state-sponsored threat actors from China and Iran are leveraging large language models (LLMs) like ChatG...

In the cybersecurity world, the Red Team is the offensive force tasked with identifying and exploiting vulnerabilities before malicious hackers can. R...