Advanced Malware Analysis: Reverse Engineering Techniques for Security Researchers
Malware analysis has evolved into a critical discipline for combating modern cyberthreats, demanding expertise in reverse engineering, memory forensic...
281 articles on cybersecurity tips, tutorials, and beginner guides.
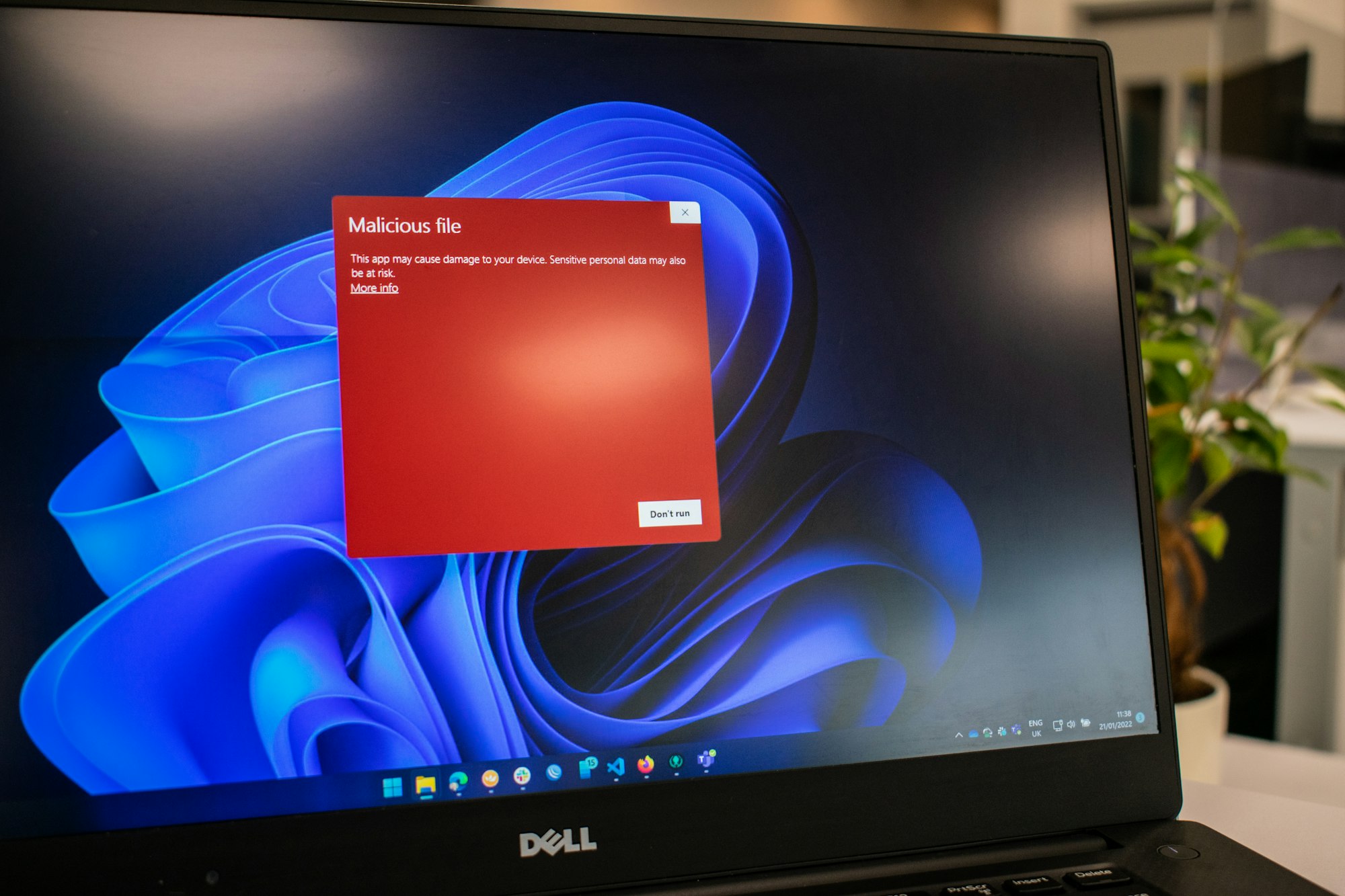
Malware analysis has evolved into a critical discipline for combating modern cyberthreats, demanding expertise in reverse engineering, memory forensic...

Network protocol analysis is the backbone of modern network security, performance optimization, and forensic investigations. This guide explores advan...

As artificial intelligence becomes integral to industries from healthcare to finance, securing machine learning (ML) models against evolving threats i...

This document explores advanced methodologies for browser security testing, focusing on extension analysis, vulnerability assessment, and custom tool....

Threat intelligence platforms (TIPs) have become indispensable tools for modern cybersecurity operations, enabling organizations to aggregate, analyze...

Open Source Intelligence (OSINT) has evolved into a cornerstone of modern intelligence operations, driven by technological advancements and the expone...

Modern anti-cheat systems employ increasingly sophisticated techniques to combat evolving cheating methods in multiplayer games. This analysis explore...
In the fast-paced world of cybersecurity, staying informed and connected is crucial. That's why we're thrilled to announce the launch of CyberEvents.D...
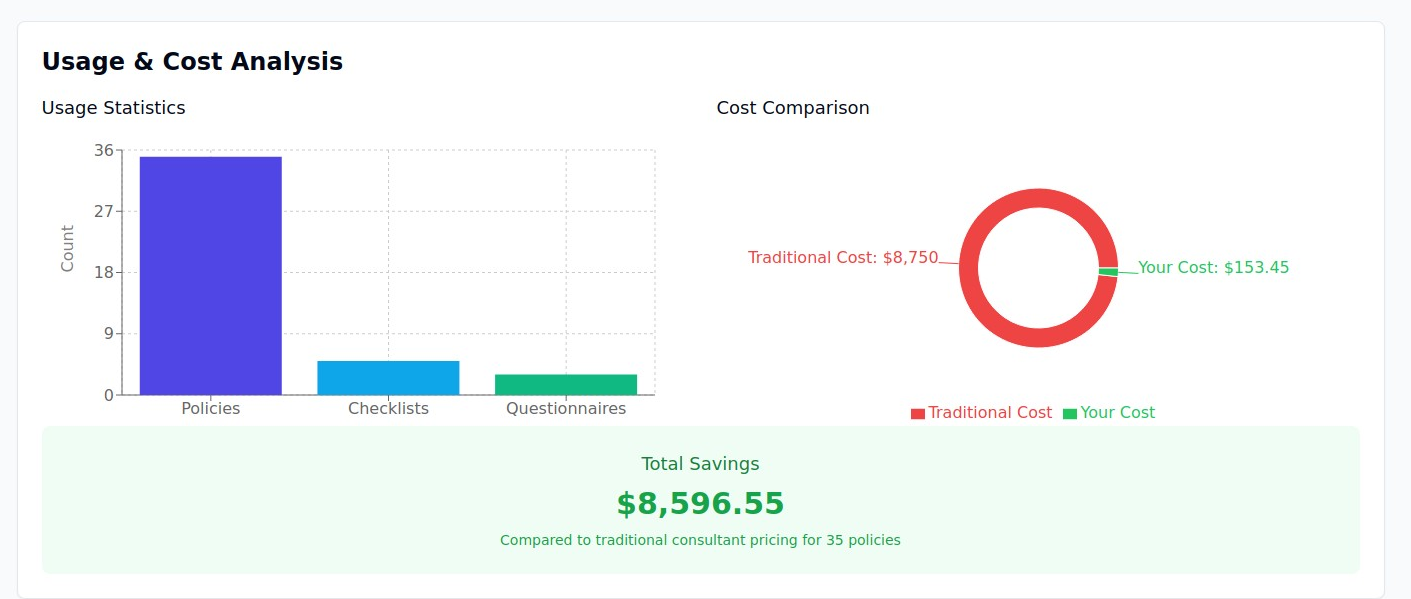
In the fast-evolving landscape of cybersecurity, organizations are required to maintain robust information security policies to comply with regulation...

Bluetooth Low Energy (BLE) has become a critical component in modern automotive systems, enabling energy-efficient connectivity while introducing new ...

Large language models (LLMs) are rapidly advancing, but safety and security remain paramount concerns. Red teaming, a simulated adversarial assessment...

Introduction As artificial intelligence continues its rapid evolution, organizations face an expanding landscape of tools, platforms, and architectura...