Fancy Bear vs Cozy Bear: Inside Russia's Elite Cyber Warfare Units
Introduction: The Hunt for the World's Most Dangerous Hackers In the shadowy world of state-sponsored cyber warfare, two names strike fear into the he...
281 articles on cybersecurity tips, tutorials, and beginner guides.

Introduction: The Hunt for the World's Most Dangerous Hackers In the shadowy world of state-sponsored cyber warfare, two names strike fear into the he...

An alarming surge in actively exploited Chrome vulnerabilities reveals sophisticated targeting by state-sponsored actors and the evolving threat lands...

In the ever-evolving battlefield of cybersecurity, understanding both offensive and defensive strategies is crucial for building robust security postu...
As artificial intelligence systems become increasingly sophisticated and interconnected, Multi-Channel Platforms (MCPs) are emerging as the backbone o...

Cyber deception has evolved significantly beyond traditional honeypots, becoming a proactive and dynamic defense strategy designed to mislead and conf...

The "Gray Man Theory" is a powerful concept for personal security during chaotic situations. It's about disappearing into the crowd so you can move un...
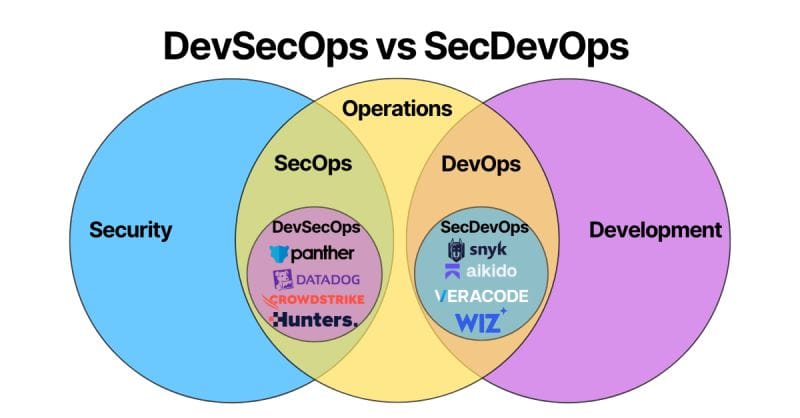
If you've ever found yourself in a meeting where people are talking about "DevSecOps" but you suspect they mean completely different things, you're no...
One of the biggest weaknesses in current API security practices is the inability to maintain accurate API inventories and monitor their usage effectiv...
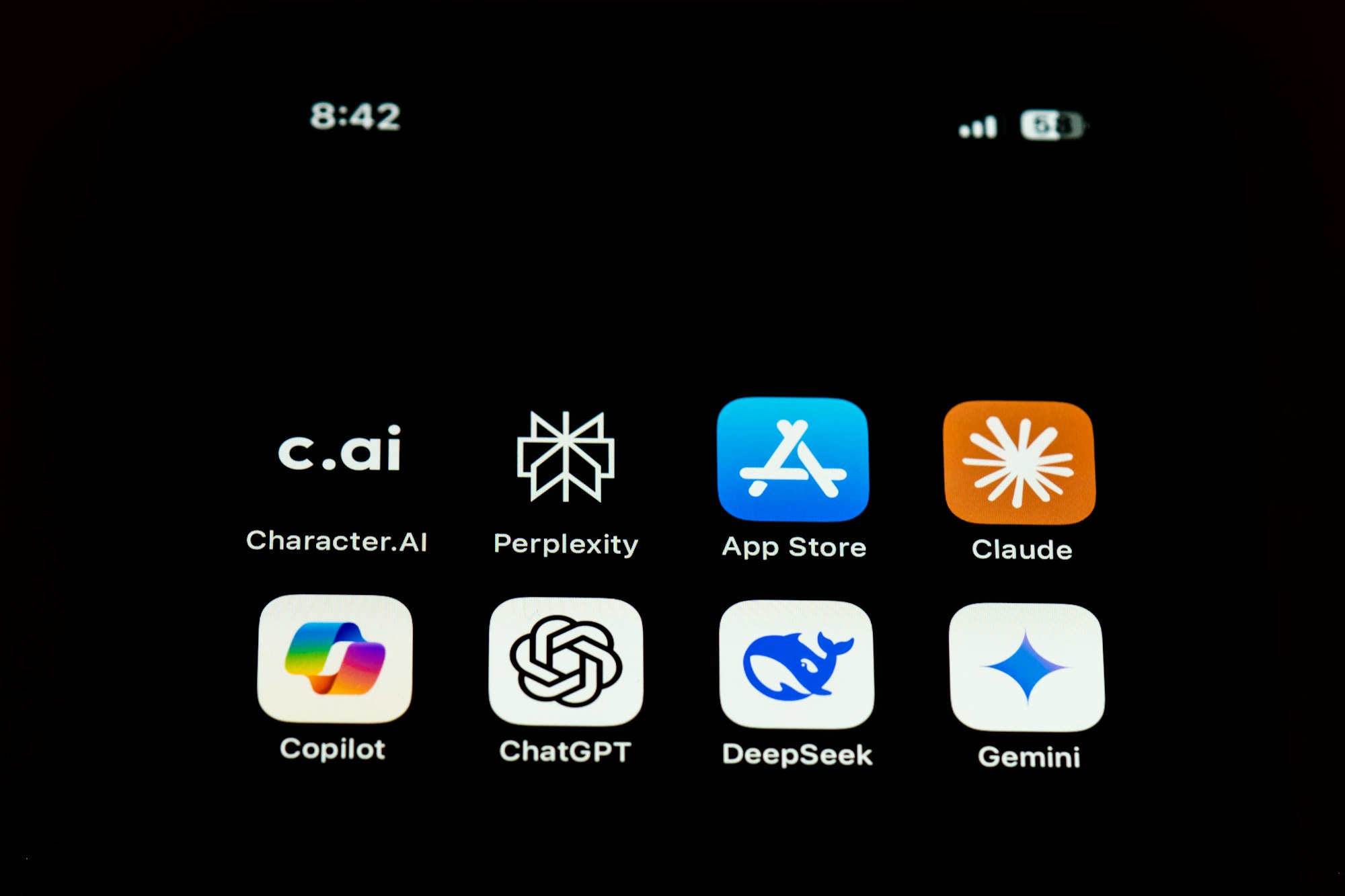
The world is buzzing about Large Language Models (LLMs) and systems like Copilot, and frankly, so are we. While security teams scramble to understand ...

The cloud computing paradigm has fundamentally reshaped how organizations operate, offering agility and scalability but also introducing dynamic and i...

Introduction Multi-Agent Systems (MAS), defined as systems comprising multiple autonomous agents coordinating to achieve shared or distributed goals, ...
Alright, fellow explorers of the digital frontier, let's talk about AI agents. Forget your basic chatbots; these things are programs designed to act o...