The Complete Guide to Firewall Types: From Noob to Pro
Think of firewalls as the digital bouncers of the internet world. Just like a nightclub bouncer checks IDs and decides who gets in, firewalls examine ...
280 articles on cybersecurity tips, tutorials, and beginner guides.
Think of firewalls as the digital bouncers of the internet world. Just like a nightclub bouncer checks IDs and decides who gets in, firewalls examine ...

Bottom Line Up Front: EA's Javelin anti-cheat system intercepted over 330,000 cheating attempts during Battlefield 6's beta weekend, showcasing both t...
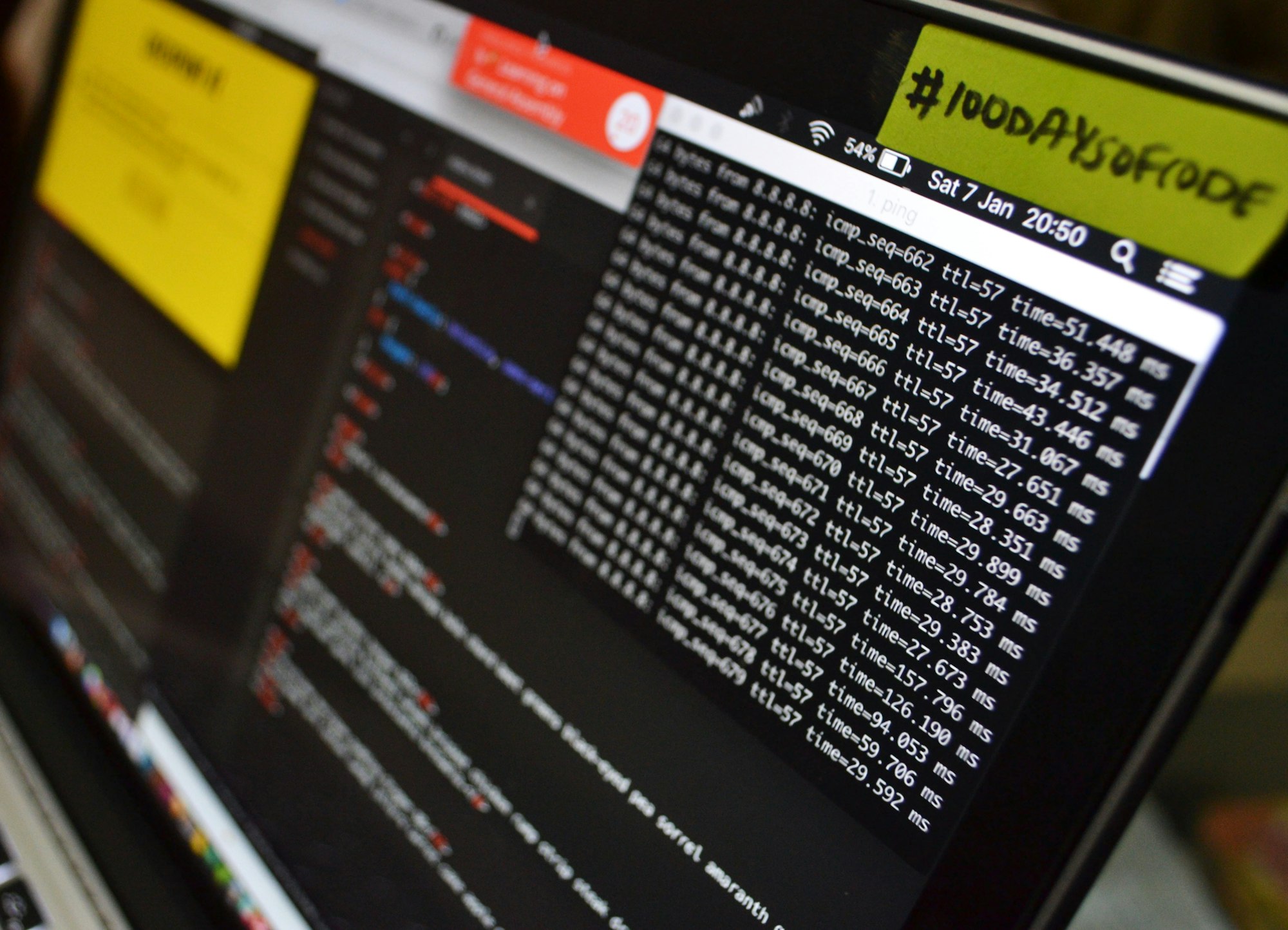
Introduction: The Game Just Changed Alright, listen up. If you're still manually querying your SIEM, copy-pasting between security tools, or clicking ...

Alex stared at the massive Las Vegas Convention Center, badge hanging around their neck, feeling like a deer in headlights. The Hacker Tracker app sho...

Executive Summary A critical security vulnerability has been discovered in the widely-used JavaScript form-data library, potentially exposing millions...

The cybersecurity landscape has undergone a dramatic transformation over the past decade, and DARPA's groundbreaking cyber challenges have both reflec...

Introduction In June 2014, DARPA launched the Cyber Grand Challenge (CGC), a competition designed to spur innovation in fully automated software vulne...

Introduction In a landmark achievement for artificial intelligence in cybersecurity, Google has announced that its AI agent "Big Sleep" has successful...

Introduction As artificial intelligence systems become increasingly autonomous and capable of taking actions in the real world, the security implicati...

Introduction: When Teenage Gamers Became America's Most Wanted Hackers In 2014, a seemingly routine border crossing between Canada and the United Stat...

Introduction: When Bedroom Hackers Embarrassed the World's Most Powerful Intelligence Agencies In 2015, the most powerful intelligence agencies in the...

Introduction: The Hunt for the World's Most Dangerous Hackers In the shadowy world of state-sponsored cyber warfare, two names strike fear into the he...