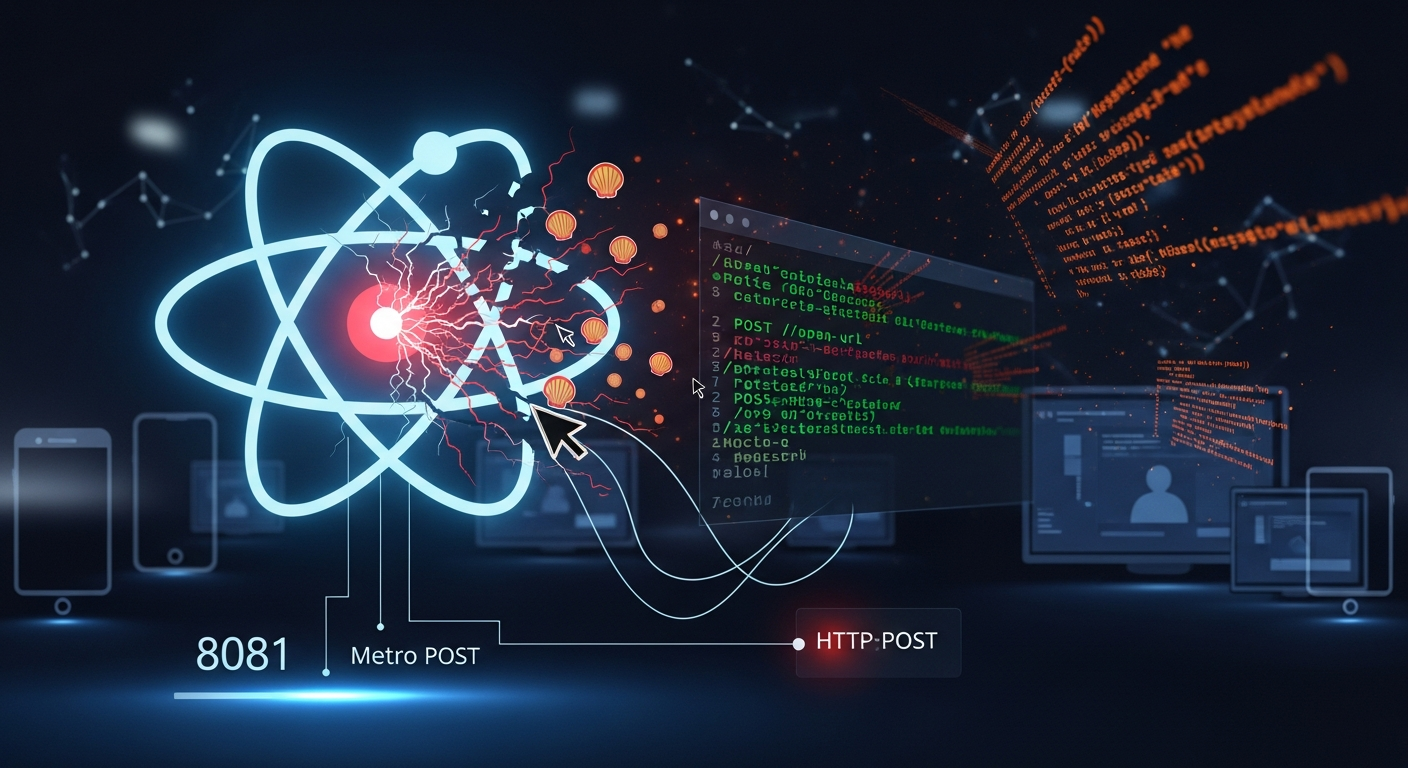
Metro4Shell: Hackers Exploit React Native CLI to Deploy Rust Malware on Developer Machines
A critical remote code execution vulnerability in React Native's Metro development server is being actively exploited to compromise developer workstat...
280 articles on cybersecurity tips, tutorials, and beginner guides.
A critical remote code execution vulnerability in React Native's Metro development server is being actively exploited to compromise developer workstat...

As AI agents gain the ability to interact with external systems, browse the web, and process user data, the attack surface for malicious exploitation ...

A Practical Guide to Complying with CISA BOD 26-02 (and Why Private Sector Should Too) The Wake-Up Call You Can't Ignore On February 5, 2026, CISA dro...

Executive Summary Google has released an emergency security update for Chrome (version 144.0.7559.132/.133), patching two high-severity vulnerabilitie...
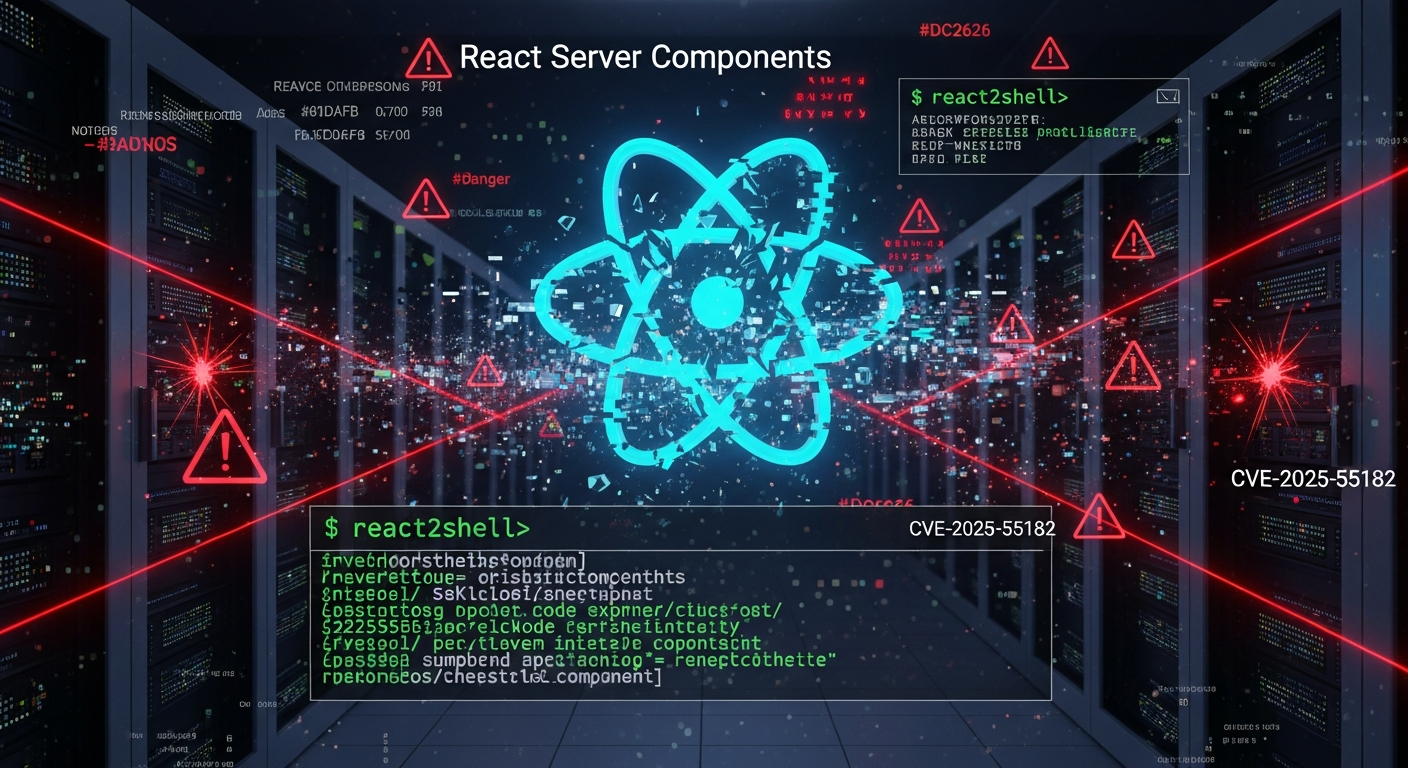
A deep dive into the CVSS 10.0 vulnerability shaking the JavaScript ecosystem—and how to protect yourself The Day React Got Owned On December 3, 2025,...

Executive Summary On January 29, 2026, Ivanti disclosed two critical zero-day vulnerabilities in its Endpoint Manager Mobile (EPMM) platform—CVE-2026-...

When one 9.9 CVSS vulnerability leads to another, and attackers target the credential vault of modern automation Executive Summary The n8n workflow au...
Your password might be weaker than you think—and artificial intelligence knows exactly why. The Wake-Up Call You Didn't Know You Needed Let me paint y...

Sam Altman announces upcoming releases will reach unprecedented AI cyber capability levels, introducing "defensive acceleration" strategy January 24, ...

Executive Summary: Groundbreaking research from Anthropic reveals that poisoning large language models requires far fewer malicious documents than pre...

Executive Summary Bulletproof Hosting (BPH) providers represent a foundational pillar of the modern cybercrime ecosystem, offering resilient infrastru...
A cybersecurity analysis of the incident that wiped a developer's entire drive and what it means for enterprise security Executive Summary On December...