The Evolution of Ethical Hacking: A Historical Perspective
In the ever-evolving landscape of cybersecurity, ethical hacking has emerged as a powerful tool in the defense arsenal. But where did it all begin? Ho...
264 articles on cybersecurity tips, tutorials, and beginner guides.

In the ever-evolving landscape of cybersecurity, ethical hacking has emerged as a powerful tool in the defense arsenal. But where did it all begin? Ho...

While high-tech cyberattacks often grab headlines, many breaches stem from a more fundamental vulnerability: human psychology. Social engineering expl...

In the vast realm of cyber threats, Distributed Denial of Service (DDoS) attacks stand out for their sheer power and potential to cause widespread dis...

Introduction The Internet of Things (IoT) is revolutionizing the way we interact with the world around us. From smart homes to industrial automation, ...

Introduction Machine learning is revolutionizing various industries, and cybersecurity is no exception. For ethical hackers, machine learning offers a...
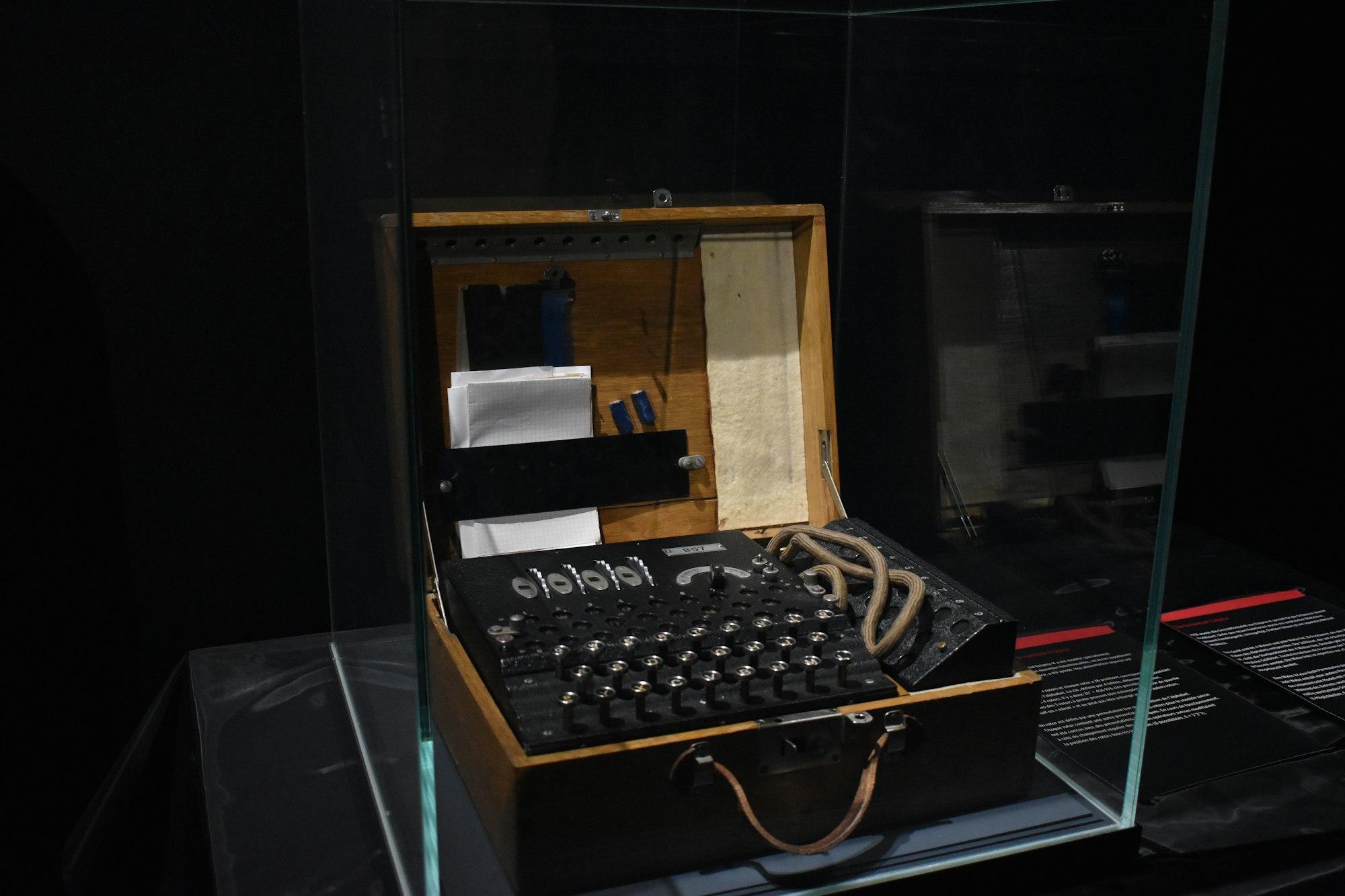
Introduction Cryptography is often seen as a complex and intimidating subject, but it's a crucial aspect of cybersecurity that hackers need to underst...

Introduction Data privacy laws such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) have significantly...
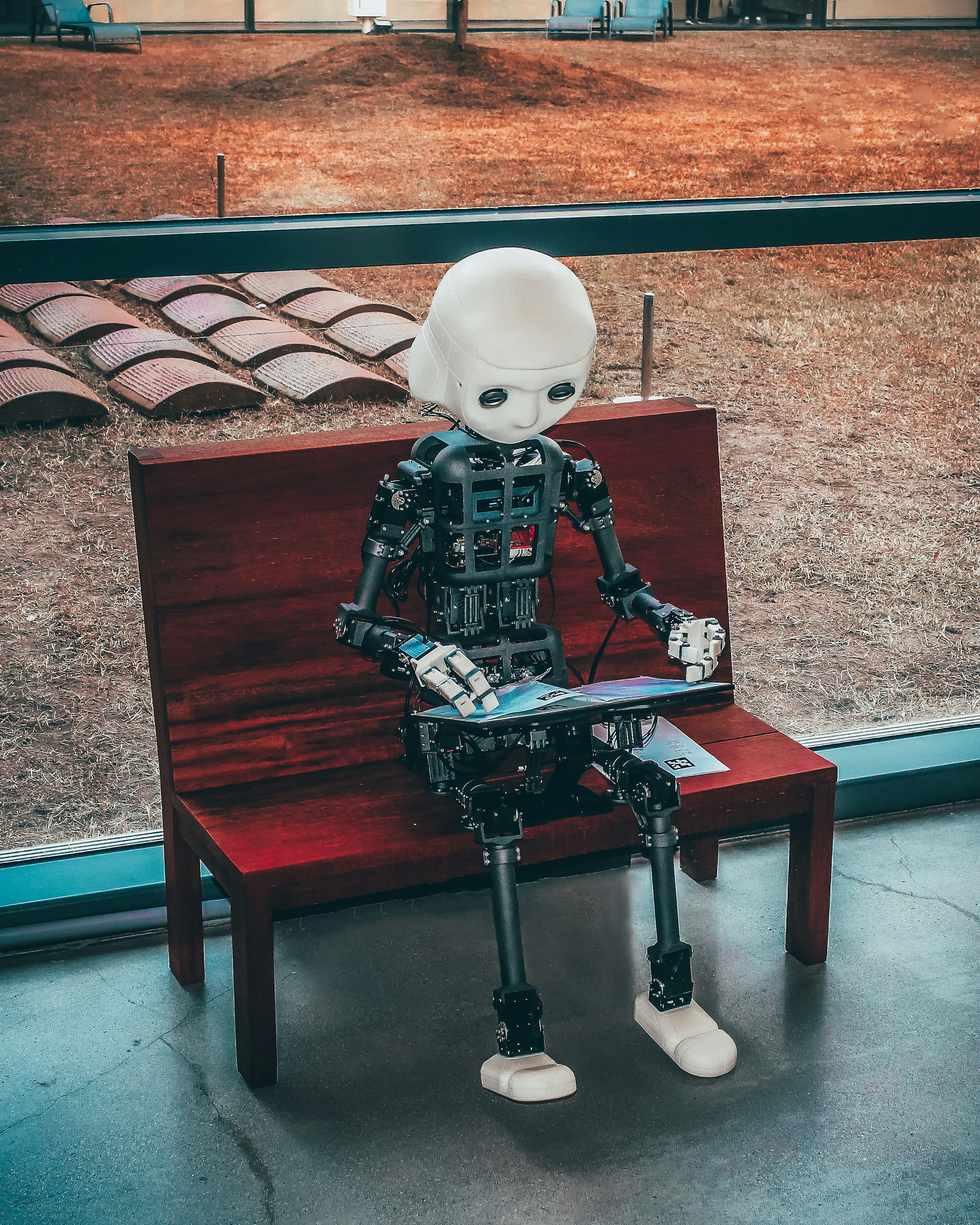
Introduction Artificial Intelligence (AI) is transforming various industries, and cybersecurity is no exception. From threat detection to incident res...

Introduction Ethical hacking is a rapidly growing field that allows cybersecurity professionals to identify vulnerabilities before malicious hackers c...

Introduction Phishing attacks are one of the most common and damaging forms of cybercrime. These attacks deceive individuals into revealing sensitive....

Introduction The Internet of Things (IoT) has revolutionized the way we interact with technology, bringing smart devices into our homes, offices, and ...

Introduction Penetration testing, often referred to as ethical hacking, is a crucial practice in the cybersecurity landscape. It involves probing syst...